March 15, 2024
Elevate Your Endpoint Security in 2024 with UEM Your organization’s endpoints—whether laptops, servers, or IoT devices—hold immense strategic value. Yet, poorly managed endpoints can be a ticking time bomb, draining resources and exposing vulnerabilities. That’s where Syxsense steps in, addressing two critical...
January 16, 2024
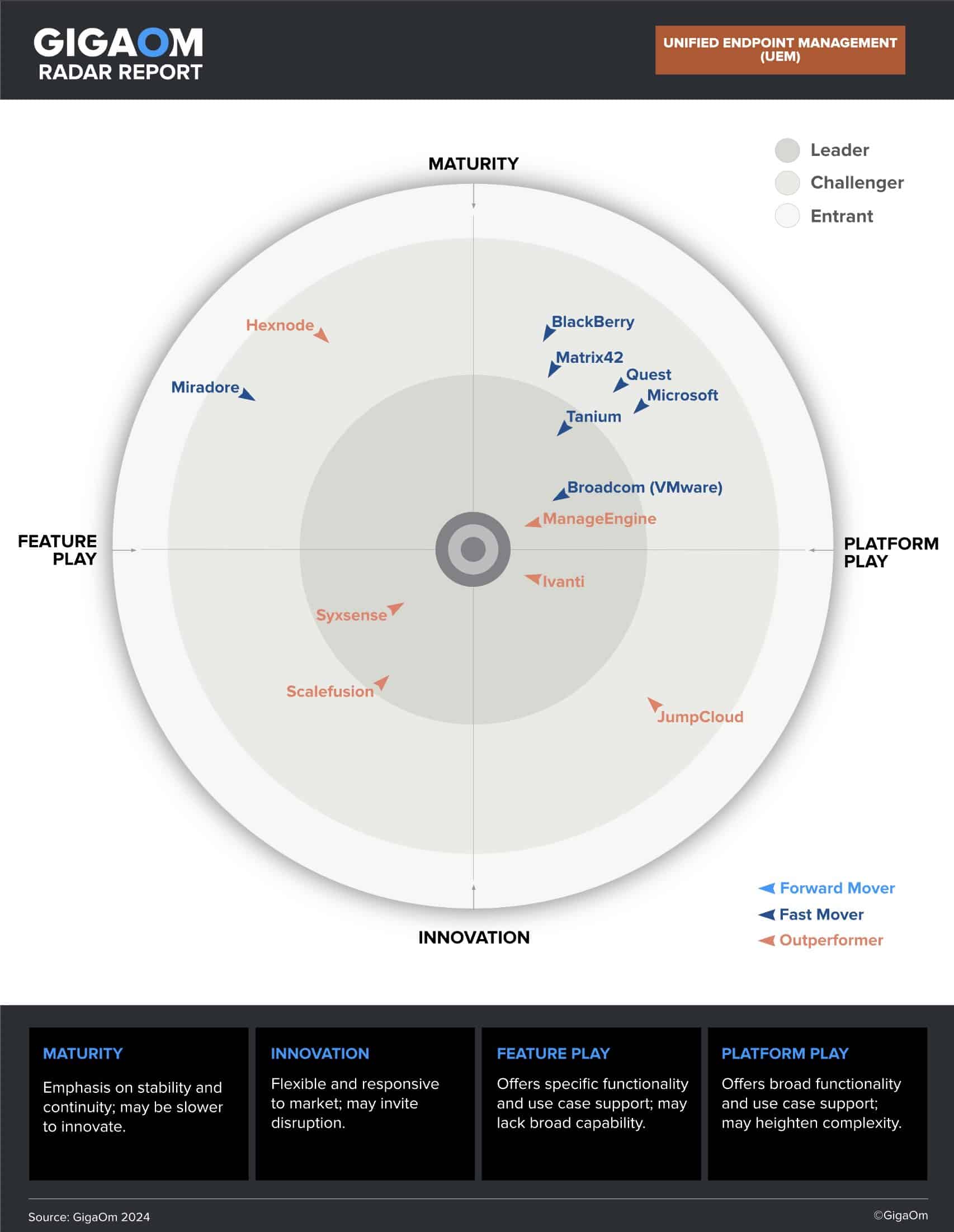
GigaOm has ranked Syxsense as a Leader and Outperformer again! Following a top ranking in the GigaOm Radar for Patch Management, Syxsense has been recognized as both a Leader and Outperformer in the 2024 GigaOm Radar Report for Unified...
January 9, 2024
An Evaluation Guide for Technology Decision Makers You want to choose the best technology for your business. But how do you know what to look for? The GigaOm Key Criteria for Evaluating Unified Endpoint Management (UEM) Solutions report can help...
September 29, 2023
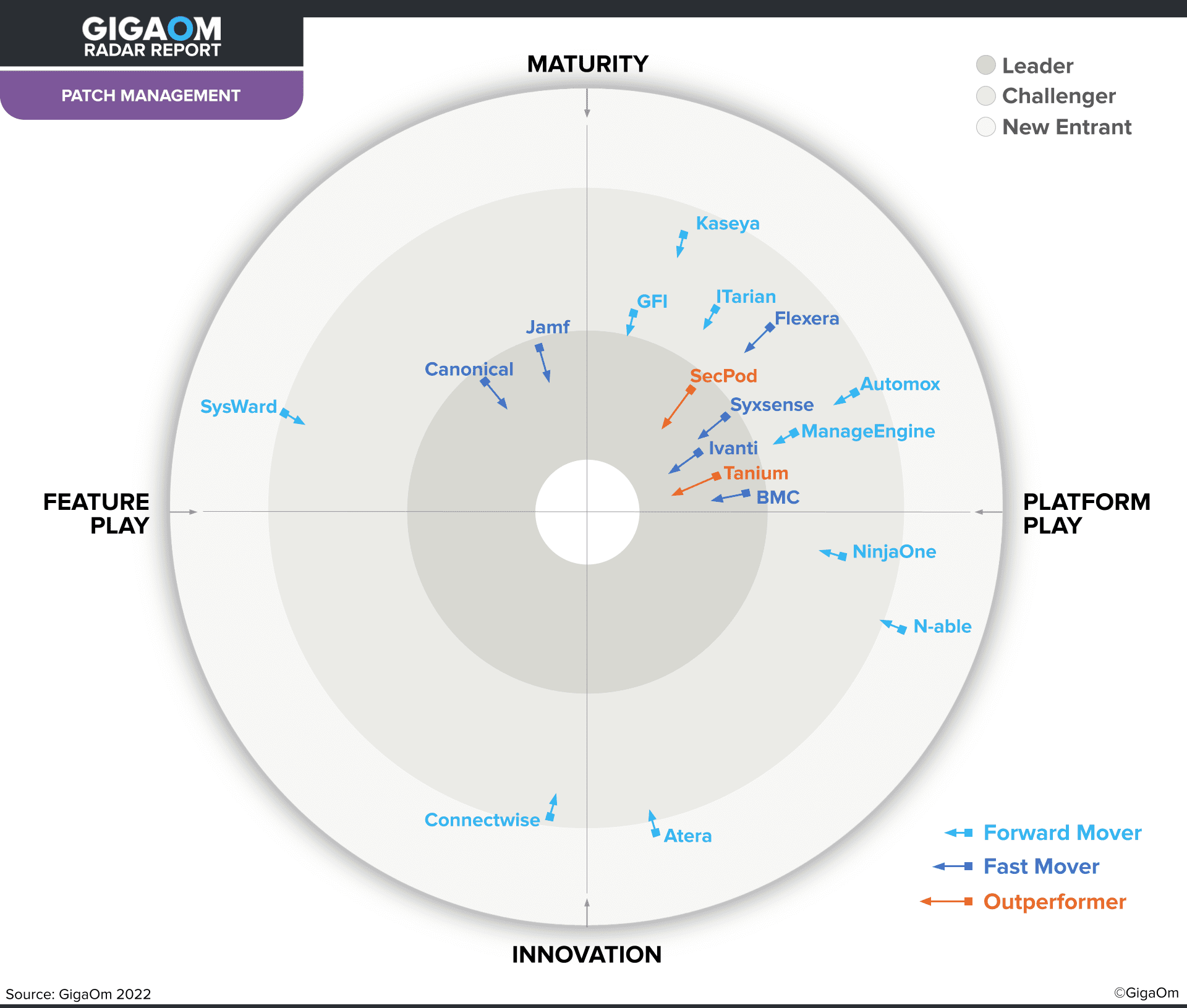
Syxsense ranked an Outperformer in 2023 GigaOm Radar Report for Patch Management Solutions We are excited to announce that Syxsense has been named an Outperformer and a Leader in the GigaOm Radar Report for Patch Management! This report is one...
April 18, 2023
Thanks for your interest in this report. It is no longer available for download. You can get the latest GigaOm report on patch management solutions here. An Evaluation Guide for Technology Decision Makers Key Criteria for Evaluating Patch Management...
January 26, 2023
Zero Trust is commonly misunderstood as a single framework that can be deployed as an out-of-the-box solution for all your cybersecurity needs. In fact, Zero Trust is a comprehensive and flexible trust model that eliminates the principle of implicit trust from...
January 1, 2023
2023 Endpoint Protection Guide Today’s threat landscape is more unpredictable than ever in the wake of the COVID-19 pandemic and the ensuing “Work From Home” and hybrid work models, leaving organizations vulnerable to an increasing number of cyberattacks. See the...
January 1, 2023
2023 Patch Management Buyers Guide Selecting a new or replacement IT management or patch management system can be difficult, with many vendors offering what seems like similar features. This guide aims to provide a list of essential questions that should...
November 28, 2022
Thanks for your interest in this report! It is no longer available for download. Check out the latest GigaOm report on patch management solutions here. Syxsense Named a Fast Mover in GigaOm Radar Report for Patch Management Solutions We...
June 4, 2021
How to Automate BitLocker Encryption For Your Business Automate Bitlocker Encryption Syxsense Cortex is the one-stop shop automation framework for managing Windows, MacOS and Linux devices. Syxsense Cortex is included in Syxsense Secure and comes with a ton of build-in...