Automated Endpoint and Vulnerability Management Software
Manage and secure your organization with an intuitive platform that automates and orchestrates every endpoint in your enterprise.
Get all the capabilities in Manage and Secure, along with pre-built vulnerability remediations, a Zero Trust Evaluation Engine to vet, verify, and validate device posture, and an open API to enable data integrations across a range of management and security tools.
Streamlining IT Operations and Security Operations

See Everything
Get all the benefits and capabilities of Syxsense Manage and Secure. Automatically find, manage, and secure all devices on your network, with cross-platform support for Windows, Mac, Linux, iOS, and Android devices.

Find, Prioritize, And Fix Your Scan for Vulnerabilities
Identify and eliminate OS and security vulnerabilities quickly and efficiently with real-time monitoring and automated scanning and remediation with pre-built, tested resolutions. Get access to our extensive library of pre-built Cortex remediation workflow templates to secure your devices at the push of a button.

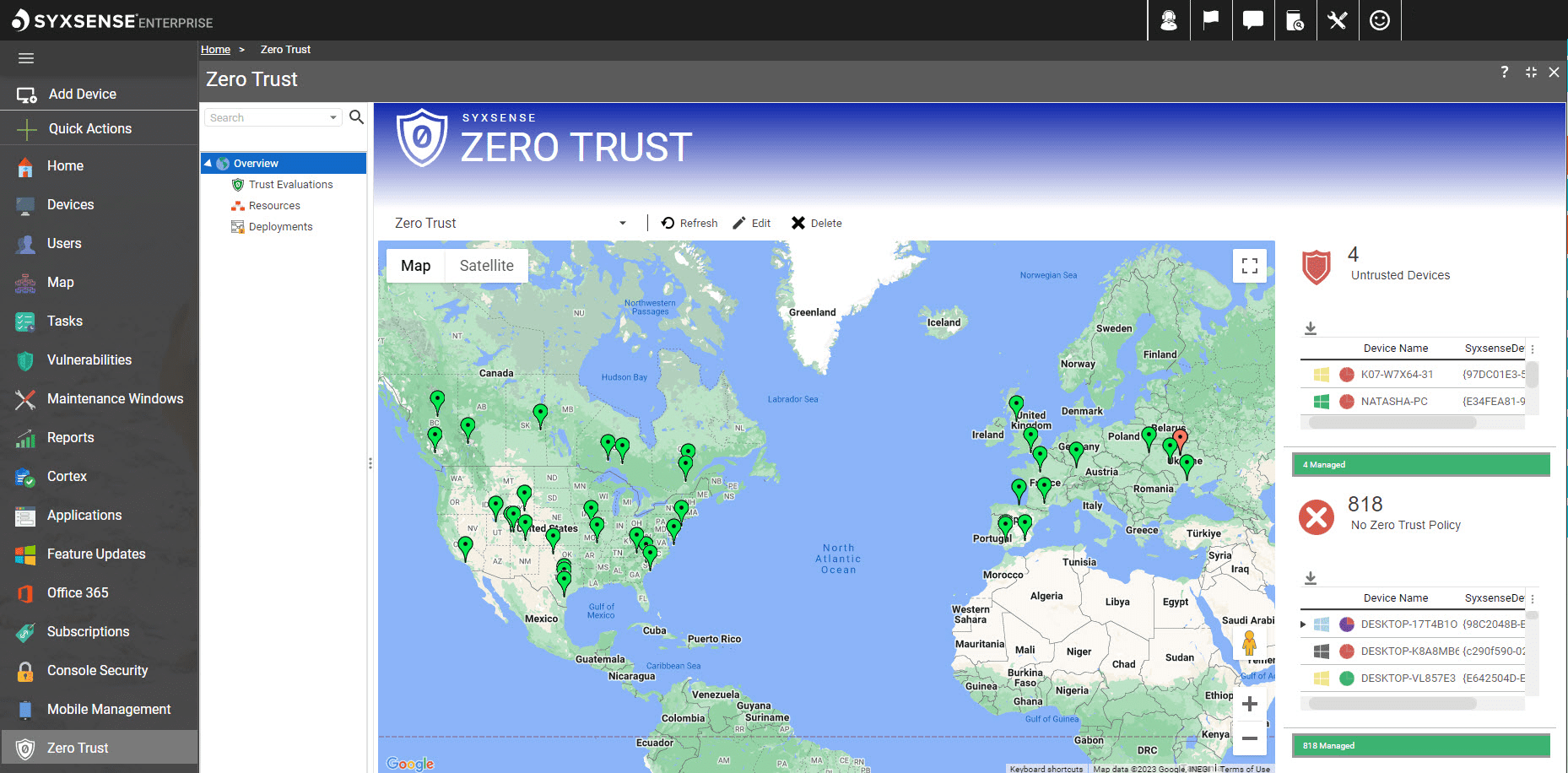
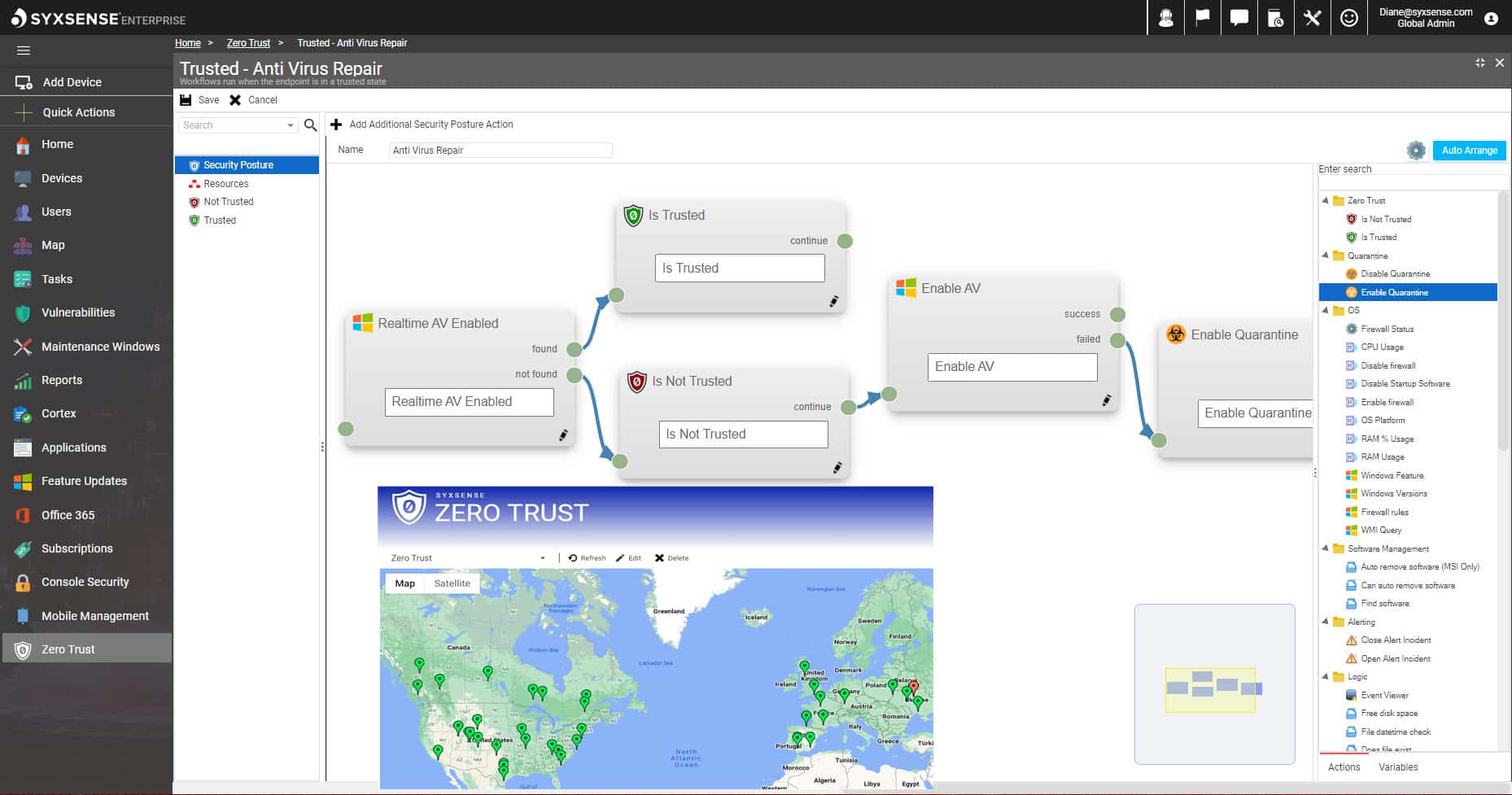
Implement Zero Trust Endpoints
Our easy-to-use Zero Trust Evaluation Engine enables you to create a trusted security posture, automate continuous validations of that security posture, and provide dynamic decisions in real-time for all your devices, saving your organization time and money and freeing up your security team to focus on more impactful projects.
As you prepare to explore the vast landscape of UEM, it’s crucial to understand which features and benefits truly matter to find the right solution for you. The 2024 GigaOm Radar Report for UEM is a comprehensive report, crafted by industry experts, which cuts through the marketing noise to reveal the true strengths and weaknesses of leading UEM vendors.
Zero Trust Endpoints
Your zero trust approach can easily extends to the endpoint, no matter where it is. With Syxsense, you can:
- Use a drag-and-drop interface to build a security profile and run that through the Syxsense Trust Evaluation Engine to determine which devices are in a secure state.
- Automatically enable or deny access to protected assets like employee data, financial information, and server infrastructure depending on the device’s current state.
- Continuously evaluate devices for trusted status, and automatically repair or remediate any risks identified to bring the device back to a compliant, trusted status.
Syxsense makes implementing a Zero Trust strategy easier and customized to your organizational policies. By building this capability to be informed by a cause-and-effect, policy-based evaluation, enterprises can have continuous Zero Trust validation for enhanced cybersecurity.
Comprehensive Endpoint and Vulnerability Management
Syxsense Enterprise includes everything in Syxsense Manage and Secure and adds pre-built security remediation capabilities, Zero Trust, and an open API. Tailor your Syxsense console to align with your security strategies to successfully avoid costly incidents, without relying on human intervention at every step.
Device Discovery, Patch, Compliance, and More
See everything within your enterprise, enabling complete management of all your IT assets – whether they are roaming, at home, on the network, or in the cloud. Customize and generate the reporting you need for executive management, auditors, and regulatory agencies.
Security Scanning & Remediation
Spot and stop critical threats early. Use our Security Scanner to find devices with OS and security vulnerabilities, weak spots, misconfiguration issues, and more. Push our pre-built (and growing) library of vulnerability remediations available in Syxsense Enterprise into our Cortex automation engine to resolve issues without any human intervention.
Drag-and-Drop Automation
Utilize Syxsense Cortex, our unique, no-code, drag and drop workflow builder to automate complex tasks, enabling thousands of devices to self-heal and self-manage.
Open API
Simplify integrations with other management and security tools with our powerful open API, enabling push/pull data transfers to ensure real-time, accurate device data informed decisions.
Our Mission
Manage and secure everything, everywhere, all the time from the cloud.
Trusted by Industry Leaders
Syxsense is proud to enable hundreds of global enterprises in reducing their IT and cyber risk with comprehensive visibility and control.
Stay a Step Ahead with the Syxsense Vulnerability Database
Syxsense’s Security Content team reviews vulnerability information and produces remediations, quickly identifying and fixing OS and security vulnerabilities so you don’t have to worry. This open-source database is available to anyone. Syxsense customers receive access to automated playbooks and scripts to easily prevent and detect potential weaknesses before they are exploited.

Join your industry peers in moving to a converged endpoint and vulnerability management platform where you can focus on your business instead of worrying about IT and cyber risk because you have both visibility and control over your infrastructure. Register Now to see the Syxsense platform in action and learn how you can manage and secure everything, everywhere from the cloud.
Unified Platform for Complete Visibility
Support Across All Platforms