Real-Time Trust Evaluation
Zero Trust Security
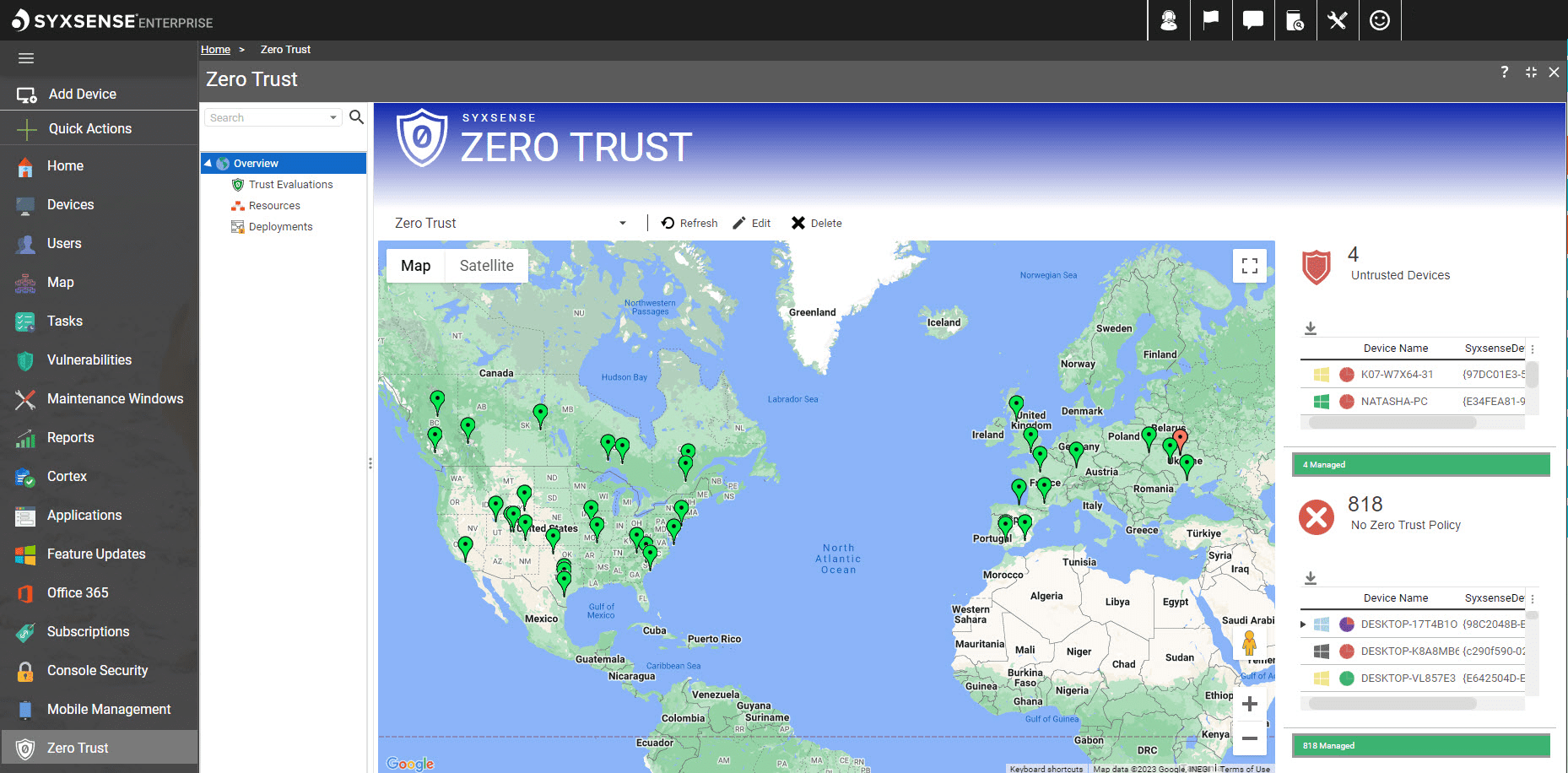
Syxsense makes implementing a Zero Trust endpoint strategy easier and customized to your organizational policies. Informed by a cause-and-effect, policy-based evaluation, enterprises can have continuous Zero Trust device attestation for enhanced cybersecurity.
Continuous Zero Trust Endpoint Validation For Enhanced Cybersecurity
Trust No Endpoint
VET
Get unparalleled, real-time visibility and control over your devices and access policies.
Verify
Check the security posture of both users and devices, measuring against a customized set of evaluations built by your team.
Validate
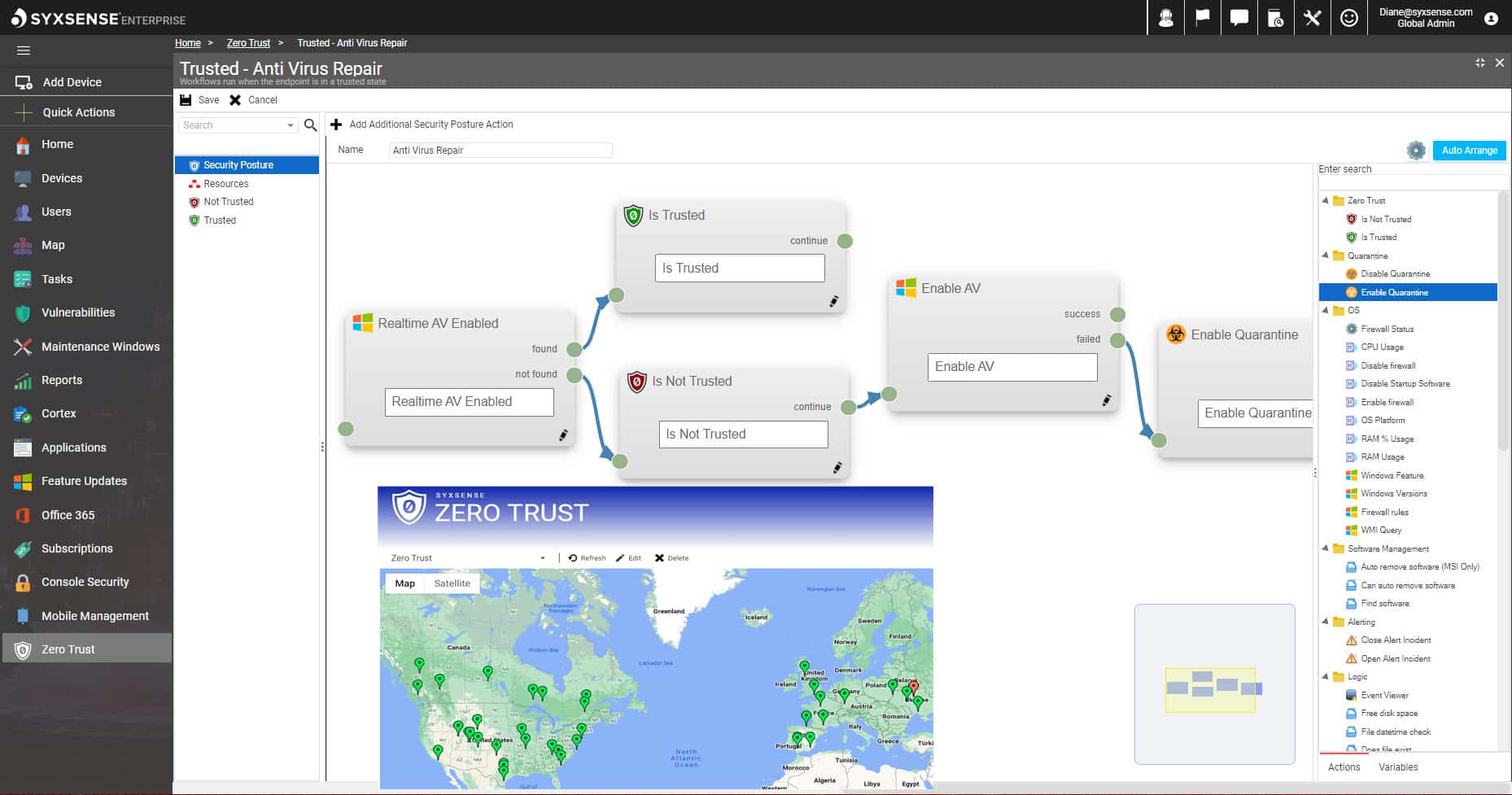
Continuously evaluate devices and automatically repair and remediate risks to bring the device back to a compliant, trusted status.
As you prepare to explore the vast landscape of UEM, it’s crucial to understand which features and benefits truly matter to find the right solution for you. The 2024 GigaOm Radar Report for UEM is a comprehensive report, crafted by industry experts, which cuts through the marketing noise to reveal the true strengths and weaknesses of leading UEM vendors.
Flexible Trust Model
Traditional security models are no longer sufficient to face the challenges of today’s threat landscape. Syxsense makes it easy to implement a Zero Trust endpoint strategy for organizations starting from scratch or for those looking to consolidate disparate tools into a single solution.
Syxsense Zero Trust endpoint security offers granular asset-by-asset control over network access policies and allows security teams to build sophisticated access policies and remediation workflows to ensure Zero Trust compliance.
Build sophisticated access policies based on a large array of configuration and security parameters and automate the immediate enforcement of access policy requirements and remediation of non-compliant devices back to trusted status.
Levels of Access
Hundreds of parameters to report and act on device compliance and block devices from accessing the network.
Enforce Compliance
Continuous user and device-based verification that grants access to corporate resources on an asset-by-asset basis.
Resolve Non-Compliance
Automatically remediation non-compliant endpoints, including patch deployment, enabling antivirus, and more.
Identity Verification
Verify trusted user authentication requests via the Syxsense console or connect with external multi-factor authentication tools to provide security status of devices.
Our Mission
Manage and secure everything, everywhere, all the time from the cloud.
Trusted by Industry Leaders
Syxsense is proud to enable hundreds of global enterprises in reducing their IT and cyber risk with comprehensive visibility and control.

Join your industry peers in moving to a converged endpoint and vulnerability management platform where you can focus on your business instead of worrying about IT and cyber risk because you have both visibility and control over your infrastructure. Register Now to see the Syxsense platform in action and learn how you can manage and secure everything, everywhere from the cloud.

Automated Endpoint Management
Syxsense Secure
Gain control over your environment with automated endpoint management, including identifying endpoint vulnerabilities, and leverage policy enforcement, immediate device quarantining, and compliance reporting to drive towards effortless business operations.

Automated Endpoint and Vulnerability Management
Syxsense Enterprise
Manage and secure your organization with an intuitive platform that automates and orchestrates every endpoint in your enterprise. Get all the capabilities in Manage and Secure, along with pre-built vulnerability remediations, a Zero Trust Evaluation Engine to vet, verify, and validate device posture, and an open API to enable data integrations across a range of management and security tools.
Unified Platform for Complete Visibility
Support Across All Platforms