April 13, 2023
The trials and tribulations of the British royal family are not the only royalty making headlines these days. The Royal ransomware group, believed to have evolved from the notorious and now defunct Conti ransomware group, is making waves across the...
April 6, 2023
The 2023 Weak Password Report once again highlighted how the breach of a password or user credential is one of the weakest links in enterprise security. When coupled with inconsistent patching, misconfigurations, and lack of vulnerability scanning, bad password practices...
March 23, 2023
Ransomware attacks against local governments are an increasingly common occurrence in recent years. According to a recent report, 330 ransomware attacks have been carried out against government systems over the past four years, with more than half a million individual...
March 17, 2023
According to a report by Comparitech, the healthcare field is attracting a lot of attention from cybercriminals; ransomware, in particular, has created chaos across the sector. In 2021 alone, there were more than 100 ransomware attacks that impacted around 2,300...
March 13, 2023
In 2022, malicious actors carried out nearly 400 ransomware attacks on U.S. organizations, affecting over 21 million individual records, according to Comparitech. With an average ransom demand of more than $4 million dollars, the cost of a ransomware attack continues...
March 7, 2023
Everyone loves a good heist movie, which is why Hollywood keeps bringing out new ones. The Ocean’s Eleven series, the Italian Job, Die Hard, the Fast, and the Furious series – the list goes on and on. Yet the story...
March 2, 2023
The profile of Common Vulnerabilities & Exposures (CVEs) has risen in recent years. Organizations now pay far more attention to them than they used to. Of course, there are still plenty of cases on record of companies getting hacked due...
February 28, 2023
NEWPORT BEACH, Calif. – February 28, 2023 – Syxsense, a global leader in Unified Security and Endpoint Management (USEM) solutions, today announced the addition of Mary Yang as Chief Marketing Officer (CMO). Yang is an experienced marketing executive that most...
February 27, 2023
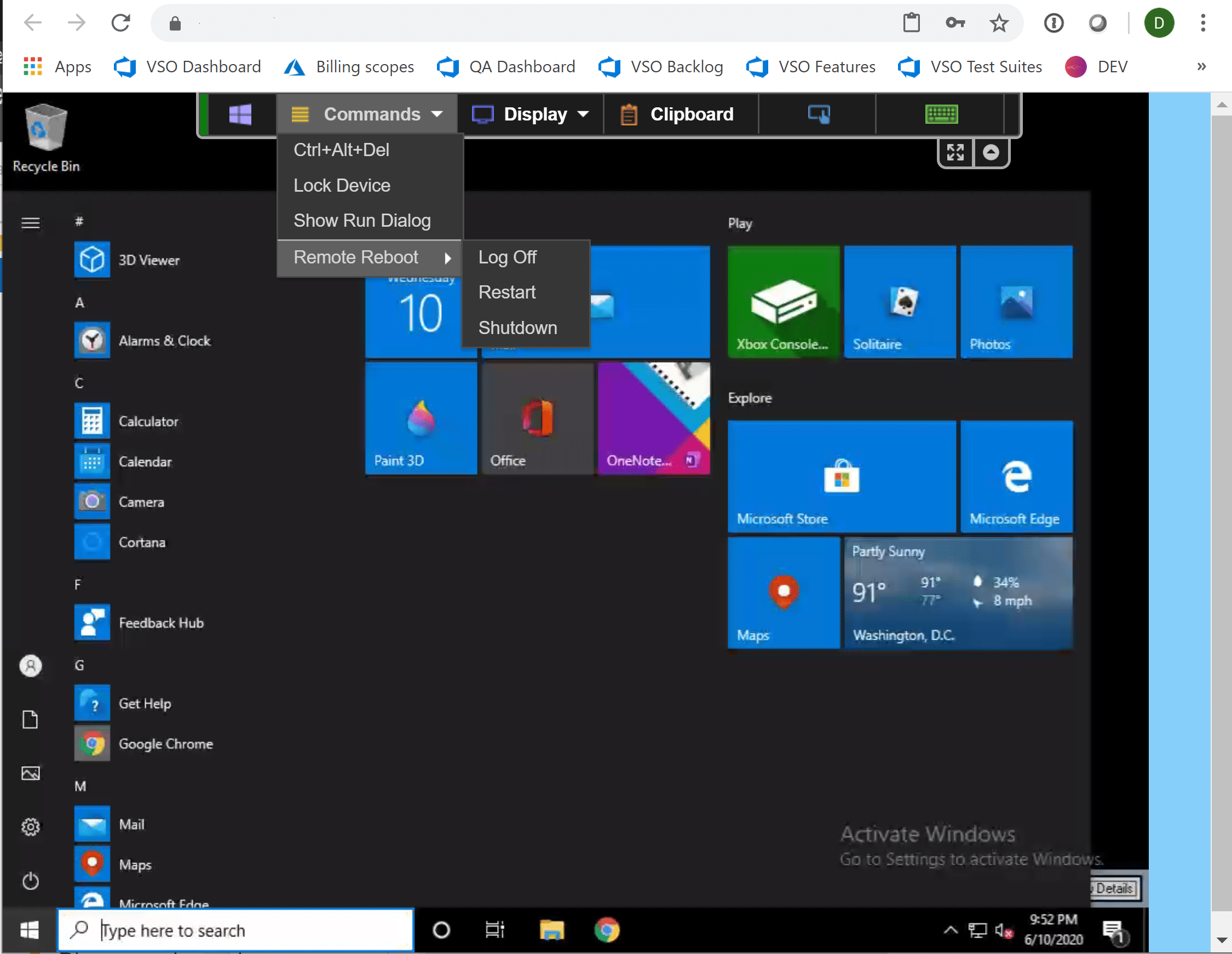
Windows users are notorious for holding onto aging operating systems and PCs many years after their sell-by date. A couple of years back, for example, an entire publishing and events office was discovered to still be running on Windows XP....
February 23, 2023
A recent survey by Foundry Research highlighted the fact that little has changed in the cybersecurity world of late. Organizations remain deeply worried about their inability to spot threats, respond to them in a timely manner, and train staff to...