Top 4 Cybersecurity Trends for 2021
Top Four Cybersecurity Trends for 2022
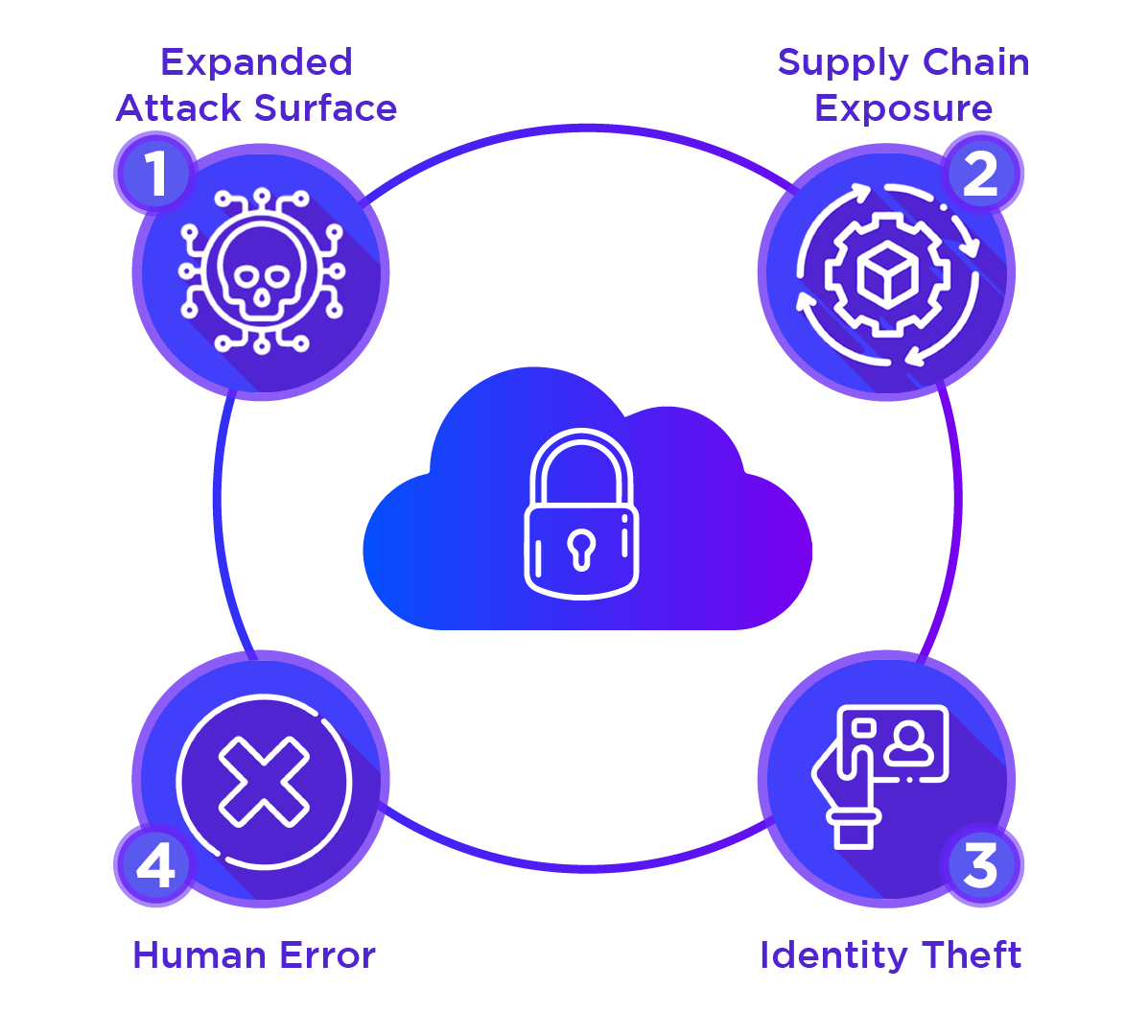
There are a great many influences at work in the cybersecurity sector, and many security trends impacting organizations. Gartner recently listed seven key trends. But let’s narrow it down further. Here are four of the top trends at play:
1. Expanded Attack Surface
Every day it seems, we hear about yet another breach, yet another zero-day vulnerability, yet another strain of ransomware. The reality is that enterprise attack surfaces are expanding. This may appear to be old news. But attack surfaces are continuing to expand, and the pace of that expansion is accelerating.
As more digitalization takes root, the Internet of Things (IoT) gains momentum, and mobility/remote platforms grow more sophisticated, it becomes tougher and tougher for IT to know what it is they are supposed to safeguard. The concept of protecting the data center and anything within the corporate firewall has been muddied by a multitude of risks. Whether it is a tighter union between IT and facility systems, a greater reliance on the cloud and open-source code, or the labyrinth that social media has become, it is harder to control enterprise assets. Thus, organizations must be more vigilant than ever and ensure their systems are fully patched so they will be able to detect anomalous behavior that may indicate a new encroachment or vulnerability.
“Organizations worldwide are facing sophisticated ransomware, attacks on the digital supply chain and deeply embedded vulnerabilities,” said Peter Firstbrook, an analyst at Gartner. “The pandemic accelerated hybrid work and the shift to the cloud, challenging CISOs to secure an increasingly distributed enterprise – all while dealing with a shortage of skilled security staff.”
2. Supply Chain Exposure
Supply chains were never easy to manage. But these days, they have turned into a nightmare. The free flow of goods from manufacturers in Asia and elsewhere has been interrupted. Ships are stuck in long backlogs at ports, and truck-based freight has been delayed due to new regulations and driver shortages. The conflict in Ukraine is going to do more than send oil and gas prices soaring. Russia and Ukraine are major producers of commodities like fertilizer and wheat. Those supplies are now shut off and the food supply of many nations is going to suffer badly as a result.
Within IT, chips, cabling, and servers are in short supply. At the same time, digitalized supply chains are under attack. The SolarWinds and Kaseya breaches highlighted the repercussions of being able to hack a provider of digital services to a large number of enterprises. Why insert malicious code in one victim at a time, when you can infiltrate the systems of a provider whose software is downloaded by a large number of sites? It’s no wonder that Gartner predicts that by 2025, 45% of organizations will experience attacks on their software supply chains.
What is to be done? Clearly, vulnerability scanning and threat monitoring efforts must be stepped up to catch incursions and strange behavior at the earliest possible point.
3. Identity Theft
Just as ransomware attackers are going after providers such as SolarWinds instead of individual organizations, those engaged in identify theft have upped their game. Yes, they still are happy to catch phishing victims randomly across the organization. But what they are really after are administrative privileges and executive/finance credentials. That’s why they are targeting identity and access management (IAM) infrastructure. They might start small, gain a user login, and then sit quietly for a while they reach up higher into the hierarchy. Credential misuse, therefore, has become a primary attack channel. Multifactor authentication and the improvement of password management can help organizations reduce the chances of a high-level identity breach.
4. Human Error
Gartner noted that human error continues to be a factor in many data breaches. Whether through clicking on malicious links or attachments, or leaving passwords on sticky notes in employee cubicles, human error is on the rise. Comprehensive security awareness training is a key aspect of defense against such errors. By educating employees on how to avoid falling victim to phishing scams and how to protect their passwords, the frequency of incursions can be greatly reduced.
That said, compromised credentials and human error are inevitable. That’s why an automated patch management and vulnerability scanning system is vital. By deploying software updates, plugging security holes, and regularly scanning for signs of malicious behavior, Syxsense provides an extra layer of protection against stolen credentials and the repercussions of human error. In a world where the attack surface has expanded and danger lurks across the software supply chain, Syxsense provides a way to keep systems free from ransomware and malware.







