March 4, 2020
Why You Need to Manage Your Endpoints Endpoint Management is More Critical than Ever Not every security or IT team has a confident endpoint management strategy. A recent survey of 1,000 IT professionals found that, while 88 percent of respondents...
March 4, 2020
How Artificial Intelligence Will Change Cybersecurity Artificial Intelligence is Growing Artificial intelligence (AI) is quickly becoming integral to our personal and business lives. A recent article on Forbes noted that, while “machines haven't taken over. . . they are seeping...
February 18, 2020
Why You Should Combine Your IT Management and Security Operations Strategy How IT Security is Changing Companies initially put up firewalls and installed antivirus software to prevent security breaches. But it wasn’t long before ransomware came along and shattered the...
February 6, 2020
Why Endpoint Detection and Response is Getting Harder in 2020 The demand for endpoint detection and response solutions across the globe is currently quite strong, with no signs of slowdown any time soon: Recent research by London-based firm Technavio predicts...
November 4, 2019
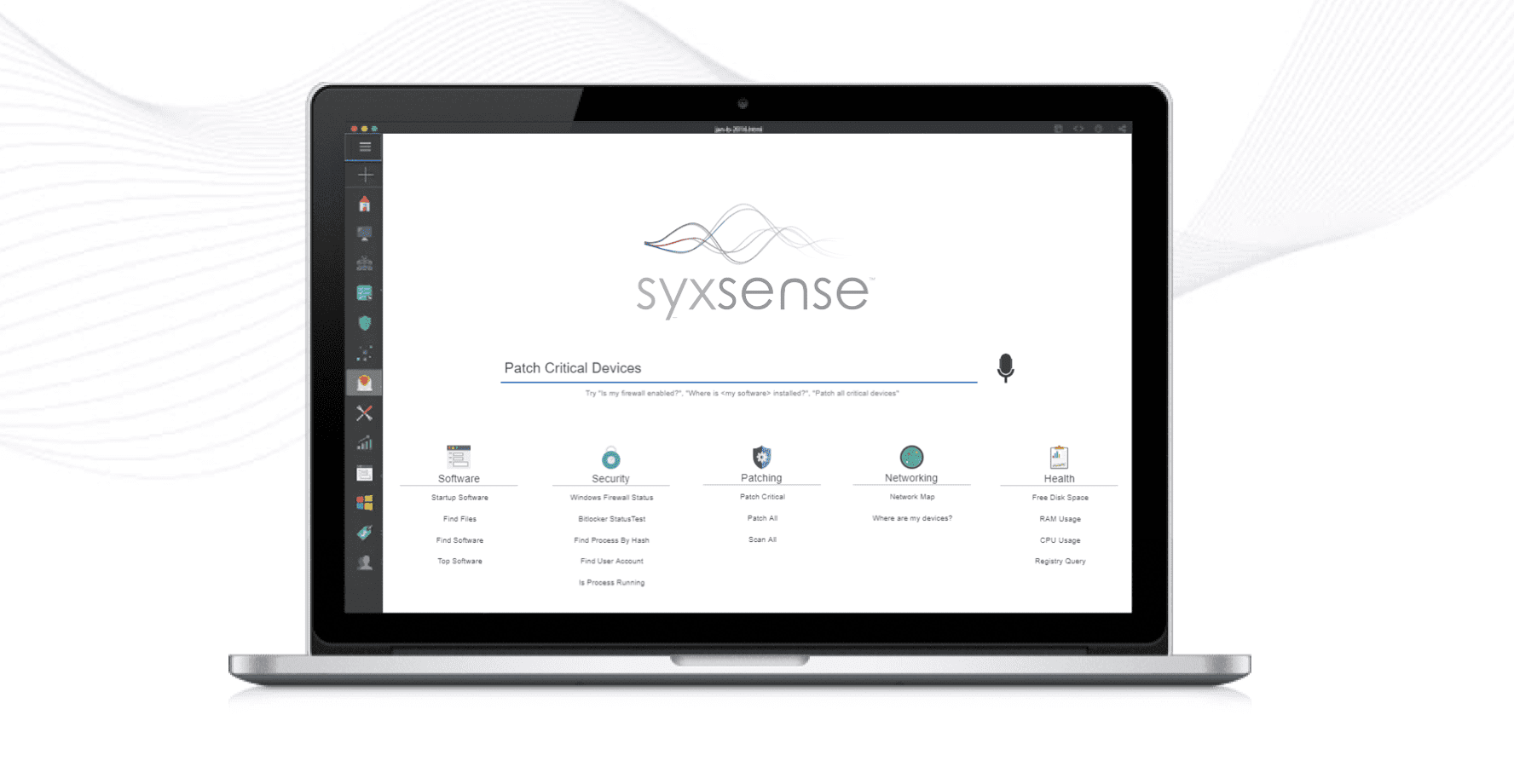
Verismic Software Launches Rebrand to Syxsense, Reinforcing its Mission to Strengthen Endpoint Security The New Name, Syxsense, Expresses Company’s Focus on Protecting the Endpoint with Powerful AI-enabled Solutions That “Know All” ALISO VIEJO, Calif. (November 4, 2019) – Verismic Software,...