October 23, 2014
Article originally featured in ITBriefcase.net The workplace trend of BYOD (Bring Your Own Device) is nothing new. What remains unclear, however, is the burden of ownership, cost and security. When employees bring their own cell phones, laptops or tablets to...
October 22, 2014
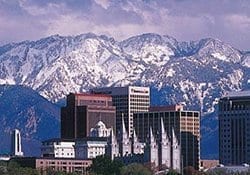
SALT LAKE CITY, UT and ALISO VIEJO, CA--(Marketwired - Oct 22, 2014) - Verismic -- a global provider of IT management solutions delivered from the cloud -- today announced the expansion of its cloud software operations with the opening of a new...
October 16, 2014
After a relatively light Patch Tuesday last month, October’s security updates are back in full swing. With a total of eight security bulletins covering a total of 24 vulnerabilities discovered in Internet Explorer, Office, and the .Net framework, three of...
October 10, 2014
Originally printed at www.btc.co.uk Ashley Leonard, President and CEO of Verismic explains his view on the imperative of simplifying Endpoint management It's now well accepted that employees use multiple devices in the workplace. Desktop PCs have been augmented with laptops,...